Stepping into the world of offensive security is exhilarating, but the CompTIA PenTest+ PT0-003 exam is a formidable gatekeeper. Unlike entry-level certs, this exam tests your ability to think like a malicious actor while acting like a professional consultant. Many brilliant IT pros fail not because they lack “hacking” skills, but because they overlook the nuances of the exam structure.
In this guide, we break down the most frequent errors candidates make from ignoring legal frameworks to failing the Performance-Based Questions (PBQs). By avoiding these traps, you’ll be better positioned to secure a high-paying role and a CompTIA PenTest+ salary that reflects your expertise.
What Is CompTIA PenTest+ PT0-003 Exam?
The PT0-003 is the latest iteration of CompTIA’s offensive security credential. It is unique because it requires candidates to demonstrate the ability to plan, scope, and manage weaknesses, not just exploit them.
CompTIA PT0-003 Exam Objectives and Structure
The exam consists of a maximum of 90 questions, delivered over 165 minutes. You’ll face a mix of traditional multiple-choice questions and immersive Performance-Based Questions (PBQs) that simulate a virtual environment. To succeed, you need a score of at least 750 on a 100–900 scale.
Skills Measured in PT0-003
The PT0-003 exam covers five critical domains:
- Engagement Management (13%): The “business” side of hacking.
- Reconnaissance and Enumeration (21%): Gathering intelligence.
- Vulnerability Discovery and Analysis (17%): Identifying the “weakest link.”
- Attacks and Exploits (35%): The core technical domain.
- Post-Exploitation and Lateral Movement (14%): What happens after the breach.
The Most Common CompTIA PenTest+ PT0-003 Exam Mistakes
Mistake #1: Ignoring the CompTIA PenTest+ PT0-003 Exam Objectives
Many students dive straight into a CompTIA PenTest+ course without looking at the official syllabus. This is like trying to build furniture without the instructions.
Why Objectives Are Your Blueprint
The CompTIA PenTest+ objectives are the only source of truth for what will be on the test. If a tool or technique isn’t in the objectives, it won’t be on the exam.
How to avoid this: Download the PT0-003 objective PDF and use it as a checklist. If you can’t explain a bullet point to a peer, you aren’t ready for that question.
- Key Takeaway: Use the official objectives as your primary study map to avoid wasting time on out-of-scope topics.
Mistake #2: Over-Focusing on Tools Instead of Methodology
A common trap is memorizing every switch for Nmap but not knowing why you are running a specific scan during the “Engagement Management” phase.
Tools vs. Techniques
The PT0-003 doesn’t just want you to know how to use Metasploit; it wants to know if you understand the exploitation lifecycle. You might be asked to interpret tool output rather than just run a command.
How to avoid this: Focus on the “why.” Instead of just learning the tool, learn the underlying protocol (like SMB, HTTP, or DNS) that the tool is interacting with.
- Key Takeaway: Tools change, but methodologies like the Cyber Kill Chain stay the same. Focus on the process.
Mistake #3: Weak Knowledge of Legal and Ethical Boundaries
In the real world, “hacking” without a contract is a crime. On the PT0-003, ignoring the “Rules of Engagement” (RoE) is a guaranteed way to lose easy points.
Compliance and Authorization Errors
You must understand documents like the Statement of Work (SOW) and the difference between various compliance standards (PCI-DSS, HIPAA, etc.). If a question asks what to do when you find data outside the agreed-upon scope, the answer is almost always “stop and report.”
How to avoid this: Study the legalities of penetration testing as seriously as you study SQL injection.
- Key Takeaway: Ethics aren’t just a “soft skill” they are a core technical requirement for professional testers.
Mistake #4: Skipping Hands-On Practice
You cannot pass the PT0-003 by reading a CompTIA PenTest+ PDF alone. The PBQs will test your ability to configure tools and analyze code in real-time.
Why Theory Alone Isn’t Enough
The exam features labs where you might have to remediate a script or configure a firewall. If you’ve never used a Linux terminal or a proxy tool, you will struggle.
How to avoid this: Use a PenTest+ simulator or set up a home lab using Kali Linux and vulnerable VMs like those from VulnHub or TryHackMe.
- Key Takeaway: Hands-on experience is the difference between a “guess” and a “correct answer” on PBQs.
Mistake #5: Misunderstanding Scoping and Reconnaissance
Candidates often rush into the “Attacks and Exploits” domain, neglecting the 21% of the exam dedicated to reconnaissance.
Planning Failures That Cost Marks
Effective recon saves time. On the exam, you may be asked about passive vs. active reconnaissance or how to handle “Scope Creep.” If you don’t understand the difference between a WHOIS lookup and a stealthy Nmap scan, you’re leaving marks on the table.
- Key Takeaway: Proper planning and reconnaissance account for over a third of your potential score when combined with management.
Mistake #6: Poor Reporting and Documentation Skills
In professional pentesting, the report is the product. The PT0-003 reflects this by testing your ability to communicate findings to stakeholders.
Reporting Is Part of the Exam
You will be tested on how to rank vulnerabilities (CVSS scores) and how to provide remediation advice. If you can’t explain to a CEO why a “Critical” vulnerability matters, you haven’t mastered the PenTest+ mindset.
How to avoid this: Review sample penetration testing reports to see how findings are categorized and prioritized.
- Key Takeaway: Technical skills get you the data; reporting skills get you the CompTIA PenTest+ salary increase.
Mistake #7: Underestimating Exploitation and Post-Exploitation
The largest chunk of the exam (35%) is Attacks and Exploits. A common mistake is only studying web vulnerabilities (like XSS) while ignoring cloud or mobile exploits.
Lateral Movement and Privilege Escalation
The PT0-003 has a heavy focus on what happens after you get in. Do you know how to use “Mimikatz” for credential harvesting? Can you explain the difference between horizontal and vertical privilege escalation?
How to avoid this: Ensure your CompTIA PenTest+ PT0-003 Study Guide covers the full spectrum of exploitation, including wireless, cloud, and IoT.
Mistake #8: Ineffective Time Management During the PenTest+ PT0-003 Exam
With 165 minutes for up to 90 questions, you have less than 2 minutes per question.
Performance-Based Question Pitfalls
Many students get “stuck” on the PBQs at the beginning of the exam and run out of time for the easier multiple-choice questions at the end.
Step-by-Step Action: How to Manage Your Exam Time
- Skip the PBQs initially: Flag them and move to the multiple-choice questions.
- Secure the “easy” points: Answer everything you know instantly.
- Return to PBQs: Spend your remaining 60-90 minutes on the simulation tasks.
- Never leave a blank: CompTIA doesn’t penalize for wrong answers, so always guess.
Key Takeaway: Protect your time. A single difficult PBQ isn’t worth 20 missed multiple-choice questions.
Mistake #9: Relying on PenTest+ Dumps Instead of Real Preparation
Using “brain dumps” is the fastest way to fail. CompTIA uses psychometrics to identify suspicious testing patterns, and the PT0-003 questions are designed to test application, not just recall.
Why Dumps Backfire
Dumps often contain incorrect answers and lack the “logic” behind the solution. Instead, use a legitimate CompTIA PenTest+ practice test to identify your weak spots.
How to avoid this: Invest in high-quality materials like an official CompTIA PenTest+ PT0-003 book.
- Key Takeaway: Authentic preparation builds the confidence needed to handle the “curveball” questions that dumps can’t predict.
Mistake #10: No Final Revision Strategy
The final mistake is stopping study the day before the exam. Your brain needs a structured “warm-up.”
Smart Revision Techniques
Don’t try to learn new topics in the final 48 hours. Instead, review your “cheat sheet” of Nmap flags, common port numbers (e.g., 445 for SMB, 3389 for RDP), and the CVSS scoring levels.
How to avoid this: Take one last CompTIA PenTest+ practice test under timed conditions to get your brain in “exam mode.”
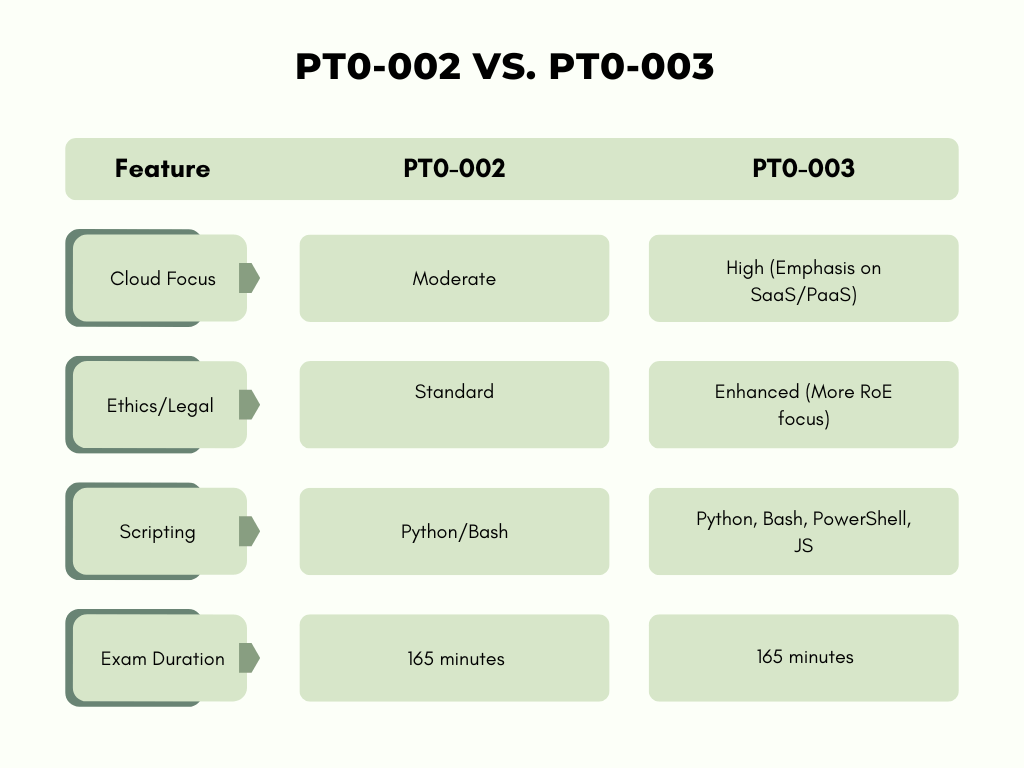
CompTIA PenTest+ PT0-002 vs PT0-003
Conclusion
The CompTIA PenTest+ PT0-003 is a milestone for any aspiring cybersecurity professional. By avoiding these ten common mistakes especially the over-reliance on tools and the neglect of legal frameworks—you set yourself apart from the average candidate. Remember, a penetration tester is more than just a “hacker”; they are a trusted advisor.
Ready to start your journey? Check out the latest PT0-003 syllabus and begin your path to certification success today.
FAQs
1. What is the CompTIA PenTest+ cost?
- The exam voucher typically costs around $425 USD, though prices vary by region and available bundles.
2. Is the CompTIA PenTest+ PT0-003 PDF worth it?
- A high-quality CompTIA PenTest+ PT0-003 PDF study guide is an excellent resource for mobile learning, provided it is from an authorized partner.
3. How hard is the CompTIA PenTest+ exam compared to CEH?
- The PenTest+ is generally considered more difficult than the CEH (Certified Ethical Hacker) because it includes Performance-Based Questions (PBQs) that require actual tool configuration.
4. What is the average CompTIA PenTest+ salary?
- According to industry data, professionals with this certification earn an average of $85,000 to $120,000, depending on experience and location.
5. Can I take the PenTest+ without Network+ or Security+?
- While not mandatory, CompTIA recommends having 3–4 years of experience and knowledge equivalent to Network+ and Security+.
6. Should I take the PenTest+ if I want to be a Security Analyst?
- Yes, understanding the “offensive” side of security helps analysts better defend against and respond to real-world threats.